Effortless Entry, Securely You.

Your Fingerprint, Your Key

Seamless Entry, Secure Exits

Security in the Cloud

Facial Recognition Pads
Unlock a new level of convenience and security. Our facial recognition devices offer fast, touch-free entry, making long lines a thing of the past. It’s a seamless and modern solution that puts your security and comfort first.

Unrivaled Convenience and Speed
Say goodbye to forgotten keys and fumbling for cards. Facial recognition provides a seamless, hands-free entry experience that gets people where they need to go faster and with less hassle. It's the ultimate upgrade in user convenience.



Contactless and Hygienic Entry
Users can gain access without touching any surfaces, making for a more hygienic and safe entry experience in today's environment.
Rapid, Hands-Free Access
Authentication takes a fraction of a second, allowing for high throughput and a smooth flow of people, eliminating the need to search for keys or swipe cards.
High-Level Security and Accuracy
Utilizes unique facial biometrics that are extremely difficult to spoof or replicate, providing a robust layer of security that traditional credentials can't match.
Prevents Unauthorized Entry
Since access is tied to a unique biological identity, it prevents unauthorized employees from clocking in for others, ensuring accurate time and attendance records.
Modern and Professional Aesthetic
The sleek design of facial recognition devices complements a modern building's architecture and creates a forward-thinking first impression for visitors.
Simple Enrollment and Management
Onboarding new users is a quick and straightforward process, and managing user permissions can be done easily through a centralized system.
Biometric access control
Replace keys and cards with the ultimate secure credential: yourself. Our biometric access control systems use unique identifiers like fingerprints to ensure that only authorized individuals can enter. It's a reliable and tamper-proof solution for any environment.

The Highest Standard of Security
With biometric access control, your security is built on something no one can replicate or steal: a person's unique physical traits. This eliminates the risk of lost credentials and unauthorized entry, giving you absolute confidence in your building's security.
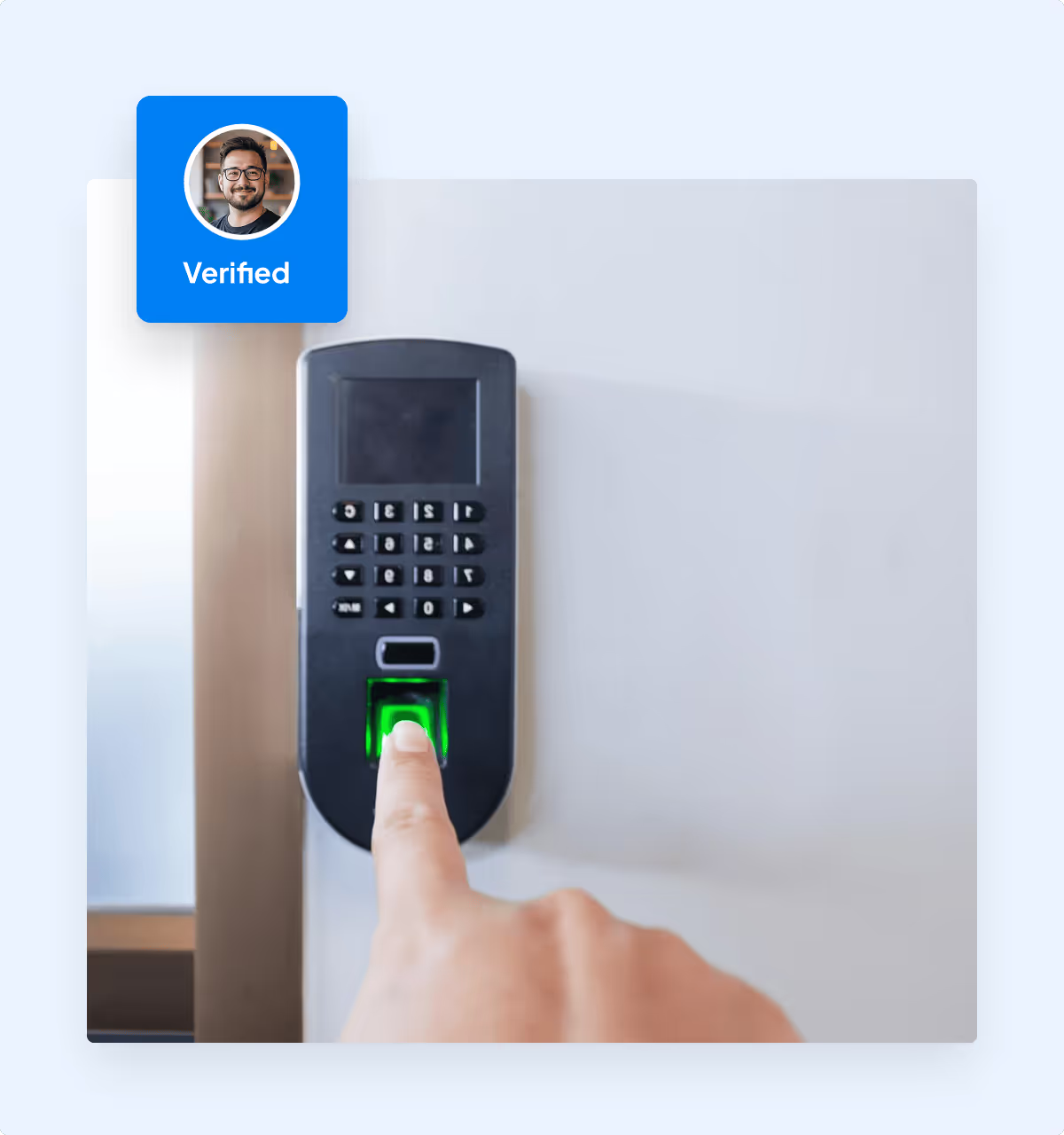
Unparalleled Security
Biometrics are fundamentally more secure than keys or cards because they are tied to a person's unique physical characteristics and cannot be lost, stolen, or shared.
Eliminates Credential Costs
There is no need to purchase, replace, or manage physical keys, fobs, or access cards, which significantly reduces long-term operational costs.
Tamper-Proof Audit Trails
Every access event is logged to a specific individual, creating an indisputable and highly accurate record for compliance and security investigations.
Highly Scalable for Any Size
No matter how many employees or visitors, biometric systems can easily scale to accommodate your organization's growth without the hassle of reissuing credentials.
Convenient for All Users
Users gain quick and convenient access with a simple touch or scan, removing the friction of remembering passcodes or carrying credentials.
Enhanced Data Protection
Protects sensitive data and assets by ensuring only authorized personnel can access secure areas, which is crucial for industries with strict regulations.
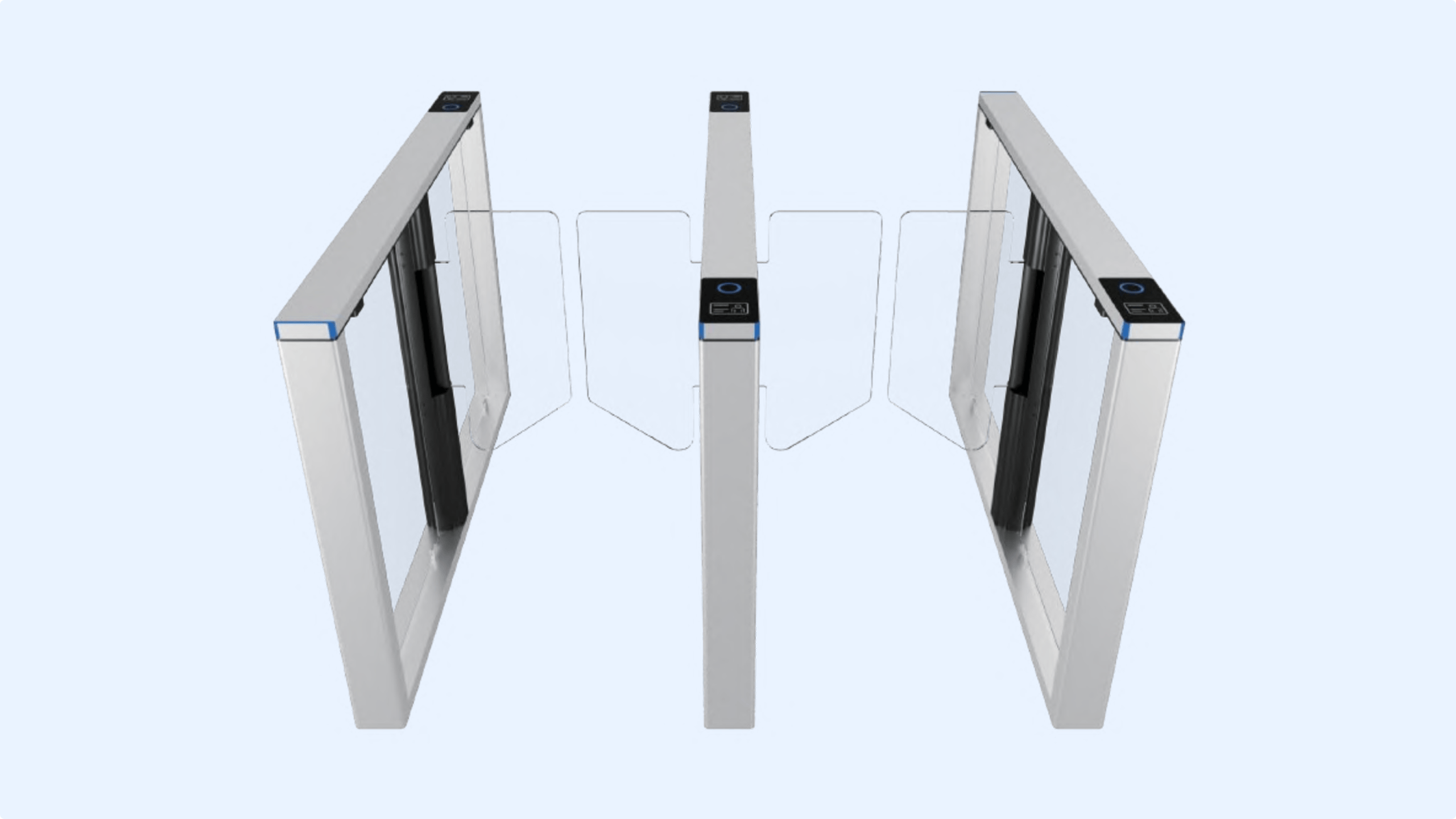
Turnstile / Speed-gate
Control the flow of people without slowing them down. Our turnstiles and speed-gates provide a clear and organized entry and exit point for your building. They are built for high-traffic areas, combining robust security with a smooth and efficient user experience.
Effortless Control of People Flow
Designed for secure rapid access, our turnstiles and speed-gates manage the movement of crowds without creating bottlenecks. They provide a clear and organized path for entry and exit, maintaining a smooth, efficient, and secure flow of traffic.


Controls High-Traffic Flow
Engineered to manage large volumes of people efficiently, preventing bottlenecks and maintaining a steady flow during peak hours.
Deters Unauthorized Access
Provides a robust physical and psychological barrier that discourages tailgating and unauthorized entry, ensuring only one person enters per valid credential.
Integrated Safety Features
Systems include emergency fire-control modes that automatically unlock the gates to allow for quick and safe evacuation.
Aesthetic and Functional Design
The modern, sleek designs with glass or stainless steel barriers can elevate the look of a lobby or entrance while still providing critical security.
Seamless Integration
Can be integrated with a variety of access control technologies, including card readers, biometric scanners, and visitor management systems.
Reduces Manned Security
Automates the entry process, which can reduce reliance on security guards for manual credential checks, allowing personnel to focus on more complex security tasks.
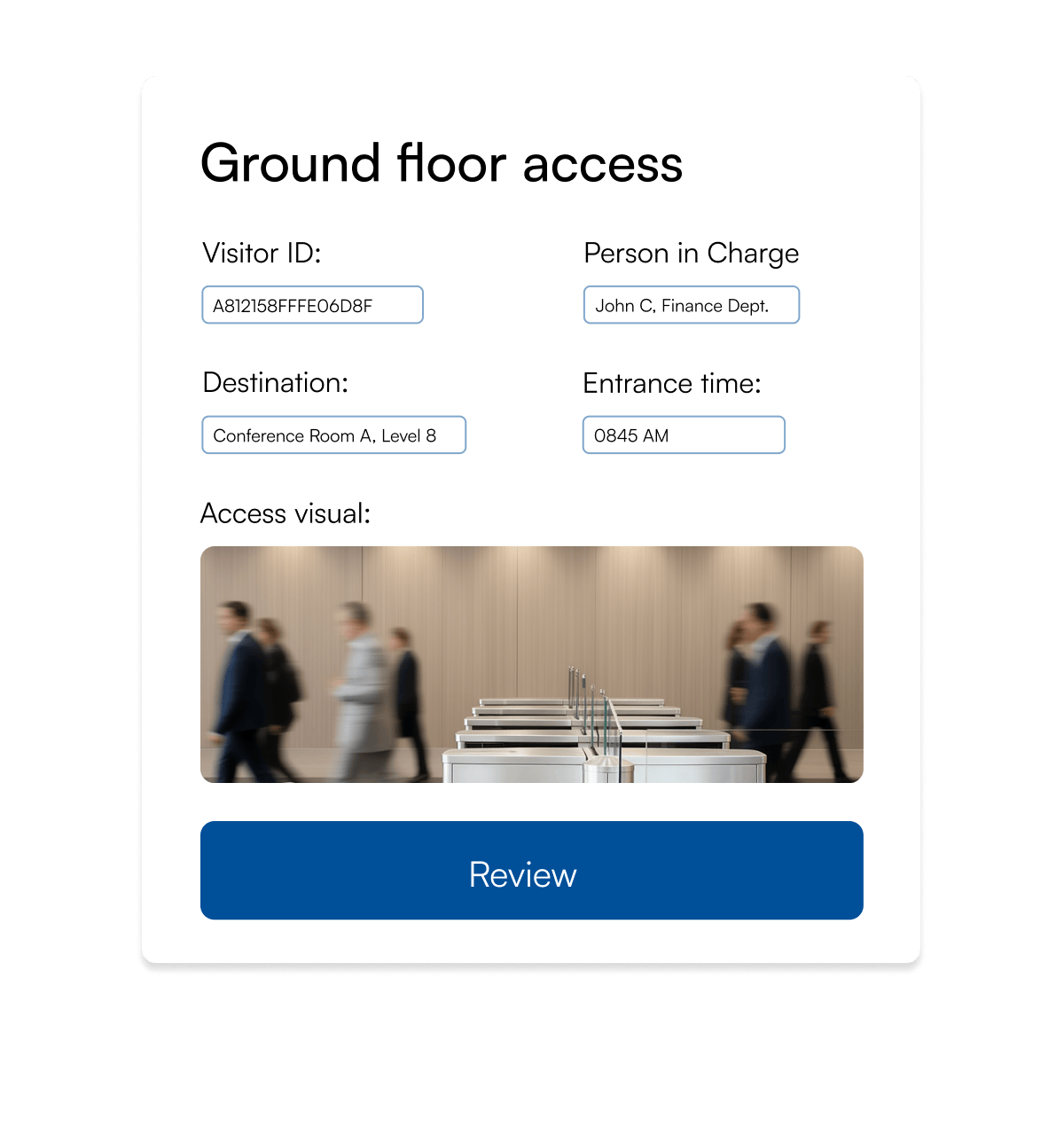
Cloud-based access control
Manage your entire security system from anywhere, at any time. Our cloud-based access control platform gives you complete control over who has access to your building, all from a simple, web-based dashboard. It's a flexible and powerful solution that simplifies security management.


Total Control, Total Flexibility
Manage your entire access control system from anywhere in the world. With cloud-based software, you can grant or revoke access instantly, view activity logs in real-time, and make changes on the fly without being tied to a physical server.

Remote Management from Anywhere
Control and monitor your entire security system from any internet-connected device, giving you real-time visibility and the ability to manage access remotely.
Simplified Scalability
Effortlessly add new users, locations, or devices as your business grows without the need for additional on-premise hardware or complex reconfigurations.
Reduced IT and Hardware Costs
Eliminates the need for expensive on-site servers and IT maintenance, transitioning your security to an economically viable model.
Automatic Software Updates
Your system is always up-to-date with the latest features and security patches, as software updates are managed automatically in the cloud.
Enhanced Security and Redundancy
Your data is stored on secure, off-site servers with multiple layers of encryption and automatic backups, protecting it from physical theft or on-site disasters.
Improved Reporting and Analytics
Gain valuable insights with detailed reporting on access events, which helps you monitor traffic patterns and make data-driven decisions about your security.
Experience our solutions. In person.
Experience our technology the way your end-users will—simple, secure, and seamless from start to finish. Walk through every interaction and see how our solutions perform in a real deployment environment.